Definitions
A smartphone is
| “ | essentially [a] computer[] integrated with radio components in a small package.[1] | ” |
| “ | [a] cell phone with a broad range of other functions based on advanced computing capability, large storage capacity, and Internet connectivity.[2] | ” |
| “ | [a] mobile computing device that provides advanced computing capability and connectivity, and runs a complete operating system and platform for application developers and users to install and run more advanced applications.[3] | ” |
A smartphone
| “ | combine[s] the telecommunications functions of a mobile phone with the processing power of a computer, creating an Internet-connected mobile device capable of running a variety of software applications for productivity or leisure.[4] | ” |
Overview
"Smartphones combine the telecommunications functions of a mobile phone with the processing power of a computer, creating an Internet-connected mobile device capable of running a variety of software apps for productivity or leisure."[5]
| “ | Because smartphones are at the boundaries of computing, telephony and telecommunications services, the lines between smartphones, mobile phones, and notebook computers have become blurred through the introduction of tablets and tablet-phone hybrids.[6] | ” |
Smartphones connect with mobile carrier networks for making calls and providing data services. Some smartphones also have the capability to connect with wireless fidelity (Wi-Fi) networks to provide data services.
In 2009, approximately 172 million mobile phones were sold in the United States. Of these, 27% were Internet-capable smartphones manufactured by a wide variety of firms, including Apple, HTC, LG, Motorola, Nokia, Palm, RIM, Samsung and Sony-Ericsson. Analysts expect smartphone sales to overtake standard mobile phone sales soon.[7]
According to Pew Research, as of October 2015, 68% of U.S. adults own a smartphone, up from 35% in 2011 when Pew Research first began examining smartphone adoption.[8]
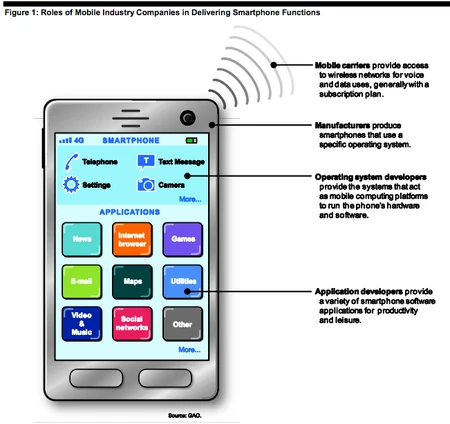
Vendors of smartphone products and services
Four types of companies are primarily responsible for smartphone products and services in the United States:
- Mobile carriers. Carriers like AT&T and Verizon provide smartphone users with access to wireless networks for voice and data uses, generally with a subscription plan.
- Operating systems. Underlying the various functions of a smartphone is an operating system that acts as a mobile computing platform to run the phone's hardware and software. Operating system developers are companies such as Apple, Google, and Research in Motion that develop the software that manages the hardware and applications of smartphones.
- Manufacturers. Smartphones are made by a variety of electronics companies. Apple and Research in Motion manufacture phones based on their own proprietary operating systems. In contrast, a number of other companies, such as HTC, Motorola, and Samsung, make phones based on the Android operating system.
- Application developers. As the popularity of smartphones has grown, so too has the number of developers offering applications for them. New mobile applications are developed every day, with some estimates indicating there are more than a million available as of mid-2012. These developers range from start-up ventures to large, established Internet companies.
Together, the products and services developed by these various companies allow users to take advantage of the various functions smartphones provide.
Security issues
Smartphones are susceptible to general networking threats and face additional security risks.
- The very portability of mobile phones and PDAs makes them easy to steal. The owner of a stolen phone could lose all the data stored on it, from personal identifiers to financial and corporate data. Worse, a sophisticated attacker with enough time can defeat most security features of mobile phones and gain access to any information they store.
- Many seemingly legitimate software applications, or apps, are malicious. Anyone can develop apps for some of the most popular mobile operating systems, and mobile service providers may offer third-party apps with little or no evaluation of their safety. Sources that are not affiliated with mobile service providers may also offer unregulated apps that access locked phone capabilities. Some users “root” or “jailbreak” their devices, bypassing operating system lockout features to install these apps.
- Even legitimate smartphone software can be exploited. Mobile phone software and network services have vulnerabilities, just like their PC counterparts do. For years, attackers have exploited mobile phone software to eavesdrop, crash phone software, or conduct other attacks. A user may trigger such an attack through some explicit action, such as clicking a maliciously designed link that exploits a vulnerability in a web browser. A user may also be exposed to attack passively, however, simply by using a device that has a vulnerable application or network service running in the background.
- Phishing attacks use electronic communications to trick users into installing malicious software or giving away sensitive information. Email phishing is a common attack on PCs, and it is just as dangerous on email-enabled mobile phones. Mobile phone users are also vulnerable to phishing voice calls (“vishing”) and SMS/MMS messages (“smishing”). These attacks target feature phones (mobile phones without advanced data and wireless capabilities) as well as smartphones, and they sometimes try to trick users into receiving fraudulent charges on their mobile phone bill. Phishers often increase their attacks after major current events, crafting their communications to look like news stories or solicitations for charitable donations. Spammers used this strategy after the March 2011 earthquake and tsunami in Japan.[9]
Privacy issues
The Communications Act of 1934, as amended, imposes a duty on mobile carriers to secure information and imposes particular requirements for protecting information identified as customer proprietary network information (CPNI), including the location of customers when they make calls. The Communications Act requires express authorization for access to or disclosure of call location information concerning the user of commercial mobile services, subject to certain exceptions.[10] Carriers must also comply with FCC rules implementing the E911 requirements of the Wireless Communications and Public Safety Act of 1999, including providing location information to emergency responders when mobile phone users dial 911.[11]
The Electronic Communications Privacy Act of 1986 sets out requirements under which the government can access information about a user's mobile phone and Internet communications. This includes legal procedures for obtaining court orders to acquire information relevant to a law enforcement inquiry.
References
- ↑ Mobility Capability Package, at 8.
- ↑ Riley v. California, 573 U.S. __ 134 S.Ct. 2473, 2480 (2014).
- ↑ Smartphone and Other Mobile Computing Device Security, at 4.
- ↑ Technology Assessment: Internet of Things: Status and Implications of an Increasingly Connected World, at 5 n.8.
- ↑ Smartphone Data: Information and Issues Regarding Surreptitious Tracking Apps That Can Facilitate Stalking, at 4 n.5.
- ↑ The Impact of the Acquisition and Use of Patents on the Smartphone Industry, at 2.
- ↑ Carolina Milanesi et al., Gartner, Inc., Forecast: Mobile Devices, Worldwide, 2003-2013, at tab 2 (Devices) (2009). The information was taken from column L (2012 year), added rows 40 (Basic Phones) and 41 (Enhanced Phones) together (95 million) and compared the number with the number received when rows 43 (Smart Phones—Entry Level) and 44 (Smart Phone—Feature) are added together (109 million). This plan contains several references to Gartner.
- ↑ Smartphone Data: Information and Issues Regarding Surreptitious Tracking Apps That Can Facilitate Stalking, at 1 n.1.
- ↑ Cyber Threats to Mobile Phones, at 3.
- ↑ 47 U.S.C. §222(f)(1).
- ↑ 47 C.F.R. §20.18.
Source
- "Vendors of smartphone products and services" section: Mobile Device Location Data: Additional Federal Actions Could Help Protect Consumer Privacy, at 3 n.5, and 4.
See also
- Feature phone
- Mobile device
- Mobile Device Location Data: Additional Federal Actions Could Help Protect Consumer Privacy
- Smartphone and Other Mobile Computing Device Security
- Smartphone data attack scenario